Historically, advertisements were limited to operating in one direction: from your newspaper, radio, or television screen to you. Enter the full duplex, bidirectional intertubes, and now advertisers have a slew of lucrative new methods to target the awful nuisance of advertisements to you. The history of sites you visit and your search history (behavioral targeting), the content of the page you’re browsing at the time (contextual advertising), and potentially all sorts of demographic and personally characterizing information may be in scope depending on the application (think e.g. Facebook).
I suppose some may, to varying degrees, not think it’s such a bad thing to have products and services offered to them that they might be interested in. But I know enough about the operators in the internet advertising space, their business ethics, and their armies of hackers ploying their ploys to be completely sickened by the idea that these organizations maintain lengthy, detailed, all but personally identifiable profiles of my web browsing habits. There is a contentious debate going on right now about the extent to which some policies and practices, on the part of some major entities like Facebook and Microsoft and Google in fact, are or are not in violation of (woefully insufficient) consumer protection laws. While all this is being sorted out, the profile they’ve got on you keeps growing, every day, every time you visit a site or fire up a search box.
Flatly, I do not care for being bombarded by advertisements, in any medium. I do not care for their cliches and their stereotypes and their lies. The secret to losing weight? Don’t want to know. Generic viagra? No thanks. Billy Mays frantically waving his hands? How about no. I think billboards cause excessive blight. I believe pharmaceutical corporations should be prohibited by law from any form of advertising and that doctors should be making those decisions for their patients, not the other way around. But I digress.
There is a certain amount of unavoidable leakage. The legitimate uses of web applications demand forking over certain details. (And what they can and cannot do with those details is the aforementioned area of contentious debate.) For instance, Facebook isn’t very useful if you don’t tell them your locale, and probably your age and gender, and maybe what school you went to. They unabashedly target advertising against all those factors, as is plain to see. There is also a certain amount of trickery that goes on involving browser bugs. The armies of hackers that work for the enemy are quite sinister, in fact, and consistently one step ahead of the armies of hackers that work for the security software companies. To wit, the ad-blocking component of a major retail internet security suite that I will not name by name was apparently dropped after several years of fighting the good fight; someone must have decided it wasn’t worth the bother any more. Then there is the oft indicated, inescapable, technically required for communication at all, numeric IP address which rarely changes even when dynamically assigned by your ISP. Though there are tools like Tor that make it possible to anonymize your network layer, I don’t use them, finding them a little overboard.
What I can recommend and what I practice on my own systems is a combination of tools and configurations that is a sane compromise, cake to implement, doesn’t break any web pages, and doesn’t make you switch to Firefox. (Unless you want to, in which case, you can, go ahead. Firefox ships with the Adblock plug-in, which is supposed to be pretty good. I would still do all steps below.) This approach relieves you from experiencing essentially all banner advertisements, and relieves the online advertising behemoths of the majority of their ability to operate in the sideband of your browsing experience building profiles about your personal browsing habits.
1. Block third-party cookies
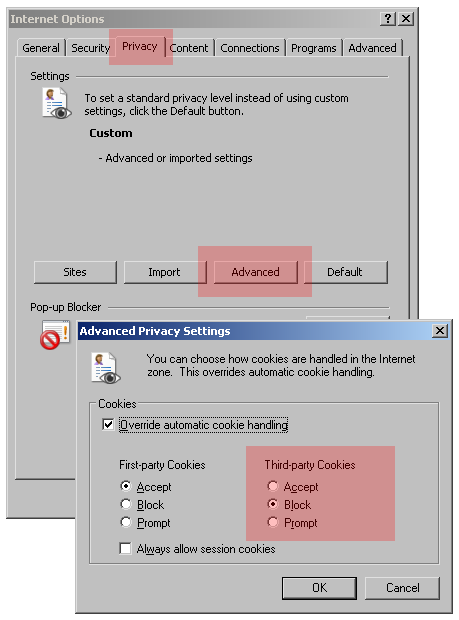
This is so simple and obvious it’s a wonder browsers don’t ship this way. It stifles the technique that the profiling systems use to identify and track your browsing activity on their central systems as you move around the web from site to site. In IE, see Tools > Internet Options > Privacy tab > press “Advanced” > put Third-party Cookies on “Block”. For the equivalent setting in Firefox, do Tools > Options > Privacy tab > uncheck “Accept third-party cookies”.
This prevents any domain that is not the one you are browsing on (the first-party) from manipulating HTTP cookies via an embedded image, script, frame, or other resource. Although due to bugs in IE it’s not airtight, it’s miles better than the default configuration, which is to blindly accept all third-party cookies. There is a full explanation over at Steve Gibson’s site as well as an assessment tool.
There is no need to block first-party cookies, in most cases necessary to operation and not up to anything nefarious. Some people with paranoid tendencies block all cookies and whitelist legitimate domains one by one, which seems tedious to me.
2. Purge accumulated tracking cookies
If you just did step 1 for the first time, unless this is a brand new system, a store of accumulated tracking cookies saved by the browser during past browsing activity still remains to be wiped out. I use Spybot for this, though there are many scanners that will detect and remove the cookies of the major offenders. The first time, it will find and remove quite a few.
I also recommend doing a follow-up scan as a regular maintenance task, say once a month, to sweep out any unlikely tracking cookies that might have slipped through the defenses. Recently my scans haven’t been turning up a single straggler, which means these methods are working. Always update Spybot to current signatures prior to scanning.
3. Block dangerous domains using the HOSTS file
In the past, I would have occupied this space with a local proxy application called the Proxomitron, however it broke a lot of web pages, was not well supported, and was cumbersome to install and update. I have found a better solution.
The MVPS Hosts File is a regularly updated blacklist of known domain names from which banner advertisements, tracking cookies, and a grab bag of other nasties are served. Leveraging the somewhat archaic configuration facility for domain name resolution at C:\WINDOWS\system32\drivers\etc\HOSTS, this method tricks Windows into redirecting any attempted network connections to all those blacklisted domains into a black hole. To install, just drop-in replace the HOSTS file with the one available on the MVPS site. To avoid a performance hit, it is strongly recommended to disable the vestigial DNS Client service from services.msc, unless you are logged in to a Domain Controller.
Be aware that, as with any ad-blocking technique, the MVPS HOSTS File will cause a very few minor peculiarities. Where banner ads were, more times than not they’re cleanly subtracted from the page, but you may get occasional red X’s too. Embedded frames that contained ads appear to render with the standard Page Not Found content. This is normal and far preferable to seeing ads. Some pages load with added latencies, probably due to the blocking of on-load ad scripting. And I get some back button annoyances, again probably a consequence of ad scripting. These side effects do not materially break any pages and are well worth the benefit of browsing ad-free. Don’t forget to go back to the MVPS site and check for an updated HOSTS file from time to time, just to stay current.
With these configurations and tools you should not see a single banner advertisement nor should your privacy be recklessly violated while browsing the web. If the software business wasn’t in cahoots with the whole frenzied consumption and consumerism zeitgeist thing, we wouldn’t have be so proactive in defending ourselves, but it is what it is. Browse safe out there.
Resources
Wikipedia: Behavioral targeting
Wikipedia: Contextual advertising
WSJ: Microsoft IE8 Browser Seeks Compromise On Privacy, Ad Growth
